In today’s digital age, mobile devices like smartphones, tablets, and smartwatches have become indispensable. Unfortunately, this widespread usage has also made them a prime target for cybercriminals. Mobile malware refers to malicious software designed to infiltrate mobile devices with the intent to steal data, spy on users, or disrupt the device’s normal functions. As this threat grows, it poses significant risks to both personal devices and corporate networks.
The Growing Threat of Mobile Malware
The rise in mobile device usage has fueled the rapid growth of mobile malware. As more people use their mobile phones for activities like banking, work, and social interactions, cybercriminals are exploiting vulnerabilities to carry out attacks. With many companies allowing employees to access sensitive corporate networks on their personal devices, mobile malware is becoming a serious concern for organizations as well. The risks are high, ranging from data theft and financial fraud to privacy invasions. Awareness and proper protection are critical.
Types of Mobile Malware
Several types of mobile malware target mobile devices. These threats vary in complexity and the damage they cause:
- Trojans: These malware disguise themselves as legitimate apps to trick users into downloading them. Once installed, they can steal sensitive data, send unauthorized messages, or give attackers remote control over the device.
- Ransomware: This type of malware locks users out of their device or encrypts their data, demanding a ransom for access restoration. It’s a growing threat that can be both costly and devastating.
- Spyware: Spyware operates in the background, quietly collecting private data such as browsing history, passwords, and call logs without the user’s knowledge.
- Adware: Though it might seem like a nuisance, adware is more than that. It floods devices with unwanted ads, slowing down performance and tracking browsing activity to serve targeted ads.
- Rootkits: These are particularly dangerous as they give attackers full control over a device’s operating system, allowing them to bypass security and hide their presence.
- Worms: Unlike Trojans, worms can spread on their own, infecting devices via messaging services, Bluetooth, or infected files. They replicate and spread rapidly, potentially causing system crashes.
- Banking Malware: Designed to target financial data, this malware can steal login credentials for banking apps and websites, leading to unauthorized access to accounts and financial loss.
- Keyloggers: These tools capture every keystroke, allowing cybercriminals to steal sensitive data like usernames, passwords, and credit card information.
- Botnets: Once infected, your device can become part of a botnet—a network of compromised devices controlled by cybercriminals to launch large-scale attacks or distribute malware.
- Hybrid Malware: A more advanced threat, hybrid malware combines multiple attack methods into one package. It can mimic Trojans, steal data like spyware, and lock files like ransomware, making it harder to defend against.
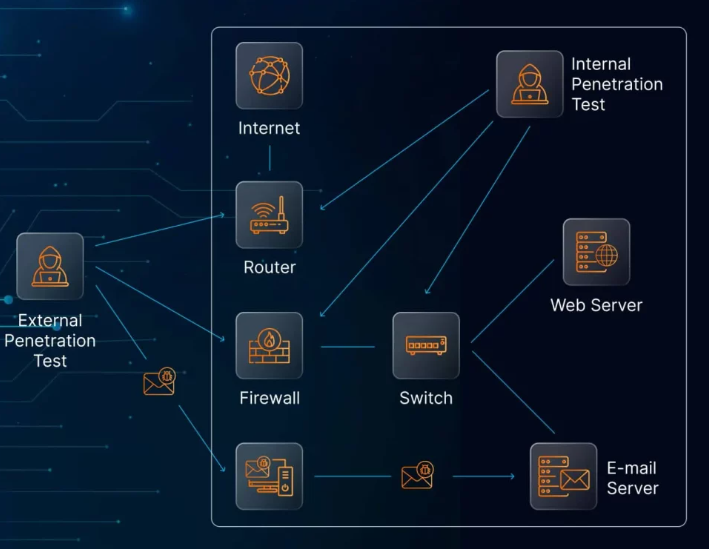
How Mobile Malware Spreads
Mobile malware is commonly distributed through various channels, including:
- SMS and Email: Malicious links or attachments in SMS messages and emails trick users into downloading malware by appearing as trusted sources.
- Social Media: Cybercriminals use social media platforms to distribute malicious links that lead to infected websites or direct malware downloads.
- Drive-by Downloads: Visiting a malicious website can trigger an automatic malware download without the user’s knowledge.
- Unsecured Wi-Fi Networks: Public Wi-Fi networks are prime targets for cybercriminals, as they can intercept data and inject malware into the connection.
- Malicious Apps: Even apps from trusted app stores can sometimes be compromised. Apps with hidden malware can steal data, track activities, or even take control of the device.
The Impact of Mobile Malware
The consequences of a mobile malware infection can be severe. Mobile malware can result in data theft, leading to the misuse of sensitive personal or corporate data. Privacy invasions are also common, as attackers gain access to private messages, photos, or location data. In addition, malware can slow down the device, causing performance issues.
For businesses, the risks include compromised systems, financial losses, and reputational damage, especially if sensitive customer or financial data is stolen.
Android vs. iOS: A Comparison of Security
When it comes to security, Android devices are more susceptible to mobile malware due to their open-source nature and the ability to install apps from third-party sources. On the other hand, iOS devices are generally more secure because of their closed ecosystem and stricter app store policies, though they are still vulnerable to phishing attacks and browser-based threats.
Android’s open nature allows more freedom for users but also increases exposure to malicious apps and malware. iOS, while more secure, can still face vulnerabilities, particularly from phishing or other social engineering tactics.
How to Prevent Mobile Malware
To protect your device from mobile malware, it’s essential to take the following precautions:
- Install Anti-Malware Software: Use security apps to detect and block threats.
- Keep Software Updated: Regular updates ensure that security patches are applied to fix known vulnerabilities.
- Practice Safe Browsing: Avoid public Wi-Fi for sensitive transactions and be cautious of suspicious websites.
- Manage App Permissions: Be mindful of which apps you install and the permissions you grant them.
- Use Strong Screen Lock Protection: This will help safeguard your device in case it’s lost or stolen.
- Educate Yourself and Others: Security awareness training can help users recognize phishing attempts and other threats.
Real-World Examples
The rise of mobile malware is evident in recent years. In 2023, mobile malware attacks surged by over 50%, with adware being the most prevalent. One example is Flubot, which targeted Android users via SMS phishing, tricking users into downloading a malicious app disguised as a package tracking service. The malware stole passwords, banking details, and contact information.
Another example is Pegasus, a sophisticated spyware developed by the NSO Group. This malware exploited vulnerabilities in mobile devices to conduct surveillance, often on high-profile targets such as journalists and activists.
Conclusion
As mobile devices become increasingly integrated into our daily lives, understanding and protecting against mobile malware is more important than ever. By taking proactive measures—such as installing security software, updating your device regularly, and practicing safe browsing habits—you can reduce your risk of falling victim to these growing cyber threats. Mobile security should be a priority to protect both your personal and professional data from malicious attacks.