Data breaches are a growing concern for businesses across all sectors, often costing millions and putting sensitive customer and company data at risk. While firewalls and encryption remain critical components of a security strategy, one of the most effective—and frequently overlooked—ways to prevent data breaches is through strategic access control. By carefully managing who has access to what information and under what circumstances, businesses can dramatically reduce the risk of both internal mistakes and external attacks.
The Importance of Access Control in Preventing Data Breaches
Data breaches often occur not because of sophisticated hacking techniques, but due to overly broad access permissions. Employees, contractors, and third parties frequently have access to more data than they need, creating weak entry points for cybercriminals and increasing the likelihood of insider misuse. By restricting access and aligning permissions with specific roles and responsibilities, businesses can create a controlled environment that minimizes the potential for unauthorized data exposure.
Did You Know?
Around 60% of data breaches are caused by insiders, whether through negligence or malicious intent, and the majority happen because users have more access than necessary.
What Are Strategic Access Restrictions?
- The Principle of Least Privilege
Employees should only be granted access to the data and systems they need to perform their job functions. This greatly reduces the damage if an account is compromised or misused. - Role-Based Access Control (RBAC)
RBAC assigns permissions based on job functions. For example, an HR associate shouldn’t have the same access to financial data as someone in the accounting department, ensuring access is role-specific across the organization. - Time-Limited and Temporary Access
For short-term projects or third-party vendor work, access should be temporary and automatically revoked once the task is completed. This helps prevent unused or forgotten accounts from becoming a security vulnerability. - Geolocation and Device Restrictions
Limiting access to specific devices, IP addresses, or geographic regions helps block unauthorized logins, especially in cases where credentials have been compromised. - Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring additional verification, ensuring that only authorized users can access sensitive systems, even if a password is stolen.
The Benefits of Strategic Access Restrictions
- Reduced Attack Surface
By limiting the systems a user can access, you reduce the number of opportunities for a cybercriminal to exploit stolen or compromised credentials. - Lower Insider Threat Risks
Whether intentional or accidental, insider threats are easier to contain when employees only have access to the data necessary for their role. - Improved Compliance
Regulations such as HIPAA, GDPR, and CMMC require strict access control measures. By implementing strategic access restrictions, organizations can meet these compliance requirements and avoid potential penalties. - Faster Incident Response
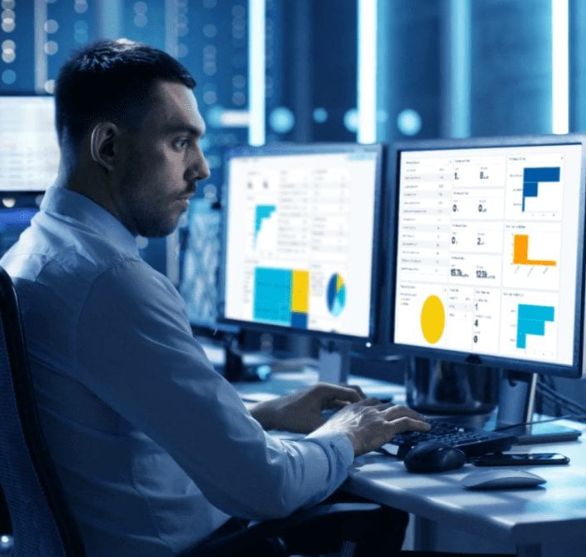
Clearly defined access rights and ongoing monitoring make it easier to track and respond to security incidents, helping reduce response times and minimize damage during a breach. - Increased Trust and Confidence
Clients, partners, and regulators are more likely to trust an organization that demonstrates strict control over who has access to sensitive data and continuously reviews and updates those permissions.
How to Effectively Implement Access Control Policies
- Audit Existing Access Permissions
Evaluate who currently has access to what data and determine whether those permissions are still needed. Remove or modify any permissions that are outdated or excessive. - Create Access Rules Based on Business Needs
Develop access policies that are tailored to each department’s specific responsibilities and workflows, limiting sensitive data exposure to those who truly need it. - Automate Access Management
Use identity and access management (IAM) tools to automate the granting and revocation of access when employees are onboarded, change roles, or leave the company. - Regularly Review Access Permissions
Conduct periodic reviews to ensure that access policies are being followed and adjust permissions as team members transition between roles or projects. - Integrate Access Control with Threat Detection
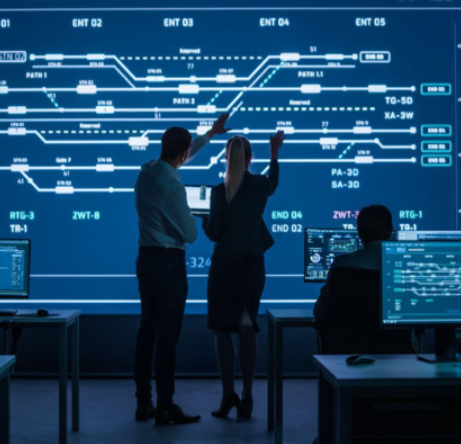
Combine access control policies with threat detection systems that alert you to unauthorized access attempts or unusual user behavior, providing an extra layer of protection.