Supply chain security is a growing concern for businesses worldwide. With the increasing reliance on third-party vendors and service providers, the risk of a supply chain attack is more prevalent than ever. In fact, recent reports show that many organizations have fallen victim to these attacks, often due to vulnerabilities in their supplier relationships. This post explores the various types of supply chain attacks, the methods hackers use to exploit these weaknesses, and the key steps you can take to protect your business.
What Are Supply Chain Attacks?
A supply chain attack occurs when cybercriminals target third-party suppliers, vendors, or service providers to infiltrate your system. These attackers often exploit weaknesses in the security measures of these external parties, allowing them to bypass your own defenses. One of the most common methods is through software updates or patches, which can be hijacked and used to distribute malicious code.
Supply chain attacks come in various forms, each with distinct tactics. These include software supply chain attacks, hardware attacks, and third-party service provider attacks, all of which can result in significant damage to your organization.
Common Types of Supply Chain Attacks
Software Supply Chain Attacks
These attacks target the development or deployment stages of software products. By injecting malicious code into software updates or third-party components, attackers can make their actions appear legitimate. Once the compromised software is installed, attackers can access sensitive information or disrupt operations.
Hardware Supply Chain Attacks
Malicious actors may also exploit vulnerabilities in hardware during the manufacturing process. For instance, they might tamper with firmware on devices such as servers or motherboards. These alterations often remain undetected until the devices are in use, providing attackers with long-term access to critical systems.
Third-Party Service Provider Attacks
Hackers can compromise a third-party service provider, such as a cloud platform or managed IT service, to gain indirect access to multiple organizations. These providers often have privileged access to systems, making them an attractive target for cybercriminals.
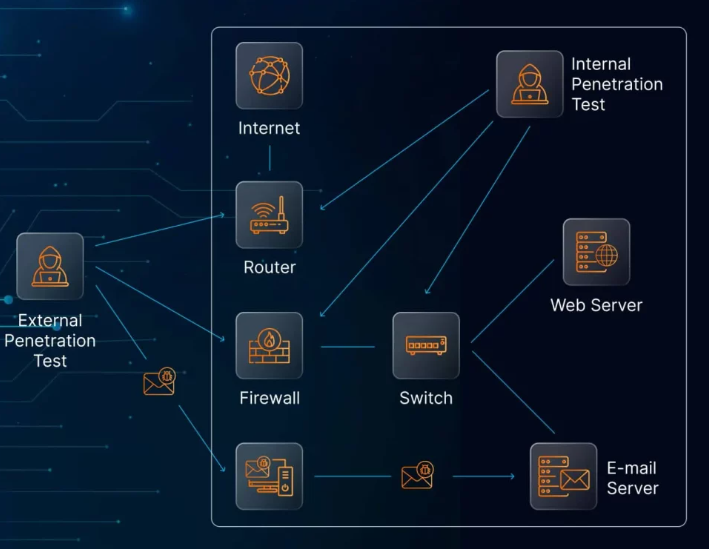
Methods Used in Supply Chain Attacks
Hackers use a variety of techniques to execute supply chain attacks. These include embedding malicious code in software updates, manipulating hardware components during manufacturing, and stealing credentials from third-party service providers. Social engineering tactics, such as phishing, may also be used to deceive vendor employees into providing access.
The most effective supply chain attacks are those that exploit trusted relationships between businesses and their suppliers. Since many companies don’t prioritize securing their vendors, these attacks can go undetected for extended periods, leading to significant damage.
Consequences of a Supply Chain Attack
The impact of a supply chain attack can be devastating. It may start with operational disruptions and escalate to financial losses, data breaches, and damage to a company’s reputation. According to recent data, the average cost of a data breach in 2024 reached a staggering $4.88 million, which represents a 25% increase over the past four years. Furthermore, the effects of a supply chain attack can ripple throughout your entire network of clients and partners.
How to Prevent Supply Chain Attacks: Key Strategies
Securing your supply chain requires proactive measures and continuous vigilance. Here are several steps you can take to protect your business:
1. Conduct Regular Supply Chain Security Audits
Start by identifying all the vendors, suppliers, and partners that have access to your sensitive data or systems. Perform thorough risk assessments to evaluate their security posture. Ensure that your vendors comply with recognized security standards and have incident reporting procedures in place. Regularly review their security practices and ensure they apply multi-factor authentication and other security protocols.
2. Establish a Third-Party Risk Management Program
Supply chain security is an ongoing process, not a one-time task. Implement a third-party risk management program to continuously assess and mitigate risks from your vendors and service providers. During vendor onboarding, evaluate their security posture and periodically reassess it. Ensure that vendor contracts include specific security obligations, such as adherence to encryption standards and incident reporting procedures.
3. Continuously Monitor Vendor Activities
Monitoring your vendors’ activities is crucial to identifying potential security breaches. Use tools such as Managed Extended Detection and Response (MXDR) or Security Information and Event Management (SIEM) systems to monitor your supply chain in real time. Regularly audit your vendors’ compliance with security requirements and contractual obligations.
4. Implement Strict Vendor Evaluation Processes
Before engaging with a new vendor, conduct a thorough evaluation of their security measures. This should include assessing their system controls, security patches, certifications, and compliance with relevant standards. Require vendors to provide evidence of security audits and adherence to industry certifications such as ISO 27001 or SOC 2.
5. Ensure Secure Software Development Practices
If you work with software vendors, make sure they follow secure software development practices. This includes incorporating security measures throughout the software development lifecycle. Vendors should perform automated code scanning to identify and fix vulnerabilities before deployment.
6. Develop an Incident Response Plan
Despite your best efforts, security breaches can still occur. Having a robust incident response plan in place is critical for minimizing the impact of a supply chain attack. Define clear roles and responsibilities for your team and vendors, and establish communication protocols for coordinating during an incident. Regularly test your plan to ensure it is effective.
7. Keep Security Policies Up to Date
Supply chain threats are constantly evolving, so it’s essential to keep your security policies current. Regularly review your policies to address emerging risks, and ensure that employees and vendors are trained on the latest security procedures.
Practical Steps for Immediate Action
To enhance your supply chain security, follow these practical next steps:
- Evaluate your current supply chain security: Review your existing security practices and identify any gaps. Are your vendors compliant with security standards? Are your access controls and encryption protocols robust enough?
- Strengthen vendor collaboration: Work closely with your suppliers to ensure they follow best security practices and meet your security requirements. Share threat intelligence and set clear expectations for security in contracts.
- Invest in continuous monitoring: Leverage advanced monitoring tools such as XDR or SIEM systems to gain real-time visibility over your supply chain. These tools can alert you to potential security issues before they escalate.
- Limit access controls: Apply the principle of least privilege to limit vendor access to only the systems and data necessary for their tasks. Periodically audit vendor access rights to ensure they remain appropriate.
- Engage with cybersecurity experts: Consider partnering with cybersecurity professionals to enhance your risk management strategy. Penetration testers can help assess vulnerabilities in your software supply chain, while a Virtual CISO can help you implement a comprehensive security strategy.
Conclusion: Securing Your Supply Chain to Protect Your Business
Supply chain attacks are a serious and growing threat to businesses around the world. With attackers exploiting weaknesses in vendor relationships, it’s essential for organizations to adopt a proactive approach to cybersecurity. By conducting thorough audits, implementing third-party risk management programs, and continuously monitoring vendor activities, you can significantly reduce the risk of a supply chain attack.
A secure supply chain not only protects your business from financial and reputational damage but also ensures the trust and confidence of your clients and partners. Start by evaluating your current practices, collaborating with trusted vendors, and investing in the tools and expertise necessary to stay ahead of attackers. In today’s digital landscape, safeguarding your supply chain is not just important—it’s critical to your business’s success.