In today’s digital landscape, cyber threats are constantly evolving, making it essential for businesses to develop cyber resilience. Cyber resiliency goes beyond simply defending against cyberattacks. It involves preparing for, detecting, responding to, recovering from, and adapting to threats quickly and efficiently, minimizing their impact on operations. A strong cyber resiliency strategy focuses on prevention, detection, response, recovery, and adaptation. Let’s take a closer look at each of these key areas and how they can protect your organization from cyber threats.
Prevention: The First Line of Defense
Prevention is the foundation of any cyber resiliency strategy. The best way to protect your organization from cyberattacks is to proactively mitigate risks before they can cause harm.
Here are some essential preventive measures:
- Network Security: Implement firewalls, intrusion detection systems (IDS), and encryption to safeguard your network. Regularly update software to fix vulnerabilities and prevent exploitation.
- Employee Training: Human error is often the weakest link in cybersecurity. Provide ongoing training to educate employees about phishing, password security, and best data protection practices.
- Access Controls: Apply the principle of least privilege, ensuring employees have access only to the data necessary for their roles. Implement multi-factor authentication (MFA) to enhance security.
- Vulnerability Management: Regularly scan for vulnerabilities using automated tools to identify and address weaknesses before they can be exploited.
Detection: Identifying Threats in Real-Time
While prevention minimizes the risk of attacks, detection plays a crucial role in identifying threats that do occur. Real-time monitoring allows you to detect breaches or anomalies quickly and respond accordingly.
Key steps in detection include:
- Continuous Monitoring: Use Security Information and Event Management (SIEM) systems to analyze security data from across your network. This allows for real-time threat detection and enables swift responses.
- Behavioral Analytics: Implement AI-powered tools to track user behavior and identify unusual activity, which can help detect insider threats or malicious actions.
- Threat Intelligence: Stay updated on emerging threats, zero-day vulnerabilities, and attack methods through threat intelligence feeds, enabling proactive defense measures.
- Endpoint Detection and Response (EDR): Use EDR tools to monitor endpoints, like laptops and servers, for signs of malware or ransomware and take action to block attacks.
Response: Containing the Threat
Once a cyberattack is detected, a swift and well-planned response is crucial to minimize damage and prevent further compromise. A clear and effective response plan ensures your team can act decisively during a cyber crisis.
How to ensure an effective response:
- Incident Response Plan (IRP): Develop a comprehensive incident response plan with clearly defined roles and procedures. The plan should cover all stages of incident management, from identification to recovery.
- Communication Protocols: Establish clear communication channels for internal teams and external stakeholders. Effective communication ensures that the right people are alerted, and everyone understands their role in the response.
- Containment Measures: Quickly isolate affected systems or accounts to prevent the attack from spreading across the network.
- Forensic Analysis: After containment, conduct a forensic investigation to understand the attack’s origins, methods, and impact. This helps improve future defenses and informs recovery efforts.
Recovery: Getting Back to Normal
Despite preventive measures and quick response, cyberattacks can still disrupt business operations. Recovery is essential to restore normal business functions with minimal downtime.
Critical recovery practices include:
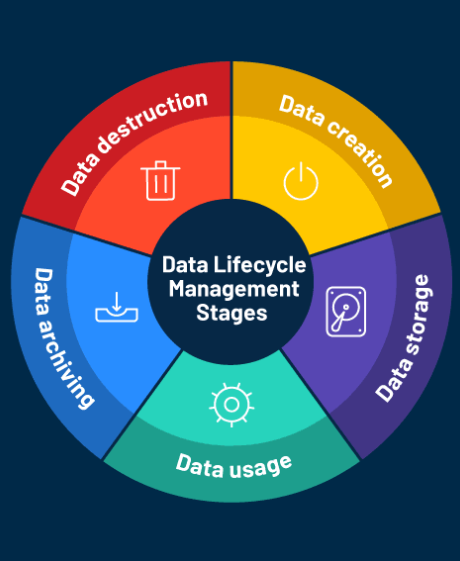
- Data Backups: Regularly back up critical data and store it securely in offsite locations or cloud storage. This ensures you can recover lost or corrupted data, especially in the case of ransomware attacks.
- Disaster Recovery Plan (DRP): Implement a disaster recovery plan that outlines how to restore vital systems and infrastructure after an attack. Regularly test this plan to ensure its effectiveness.
- System Restoration: Prioritize the restoration of essential services and systems. This may involve reinstalling software, recovering data from backups, and gradually bringing systems back online.
- Post-Incident Review: After recovery, conduct a post-incident review to assess the effectiveness of the recovery process. Identify areas for improvement to strengthen future responses.
Adaptation: Evolving to Stay Ahead of New Threats
Cyber threats are continuously evolving, and so should your cybersecurity strategy. Adaptation is an ongoing process that helps your organization stay one step ahead of cybercriminals by updating defenses to handle emerging threats.
Key strategies for adaptation include:
- Threat Intelligence Sharing: Participate in industry forums, government agencies, and cybersecurity communities to share threat intelligence. Collaborating with others helps ensure you stay informed about new threats.
- Regular Updates and Patching: Regularly update software, hardware, and applications to address vulnerabilities and ensure security patches are applied promptly.
- Continuous Improvement: Use lessons learned from past incidents to refine your cybersecurity policies, training programs, and tools. Continuously assess and improve your security posture to adapt to new threats.
- Emerging Technologies: Leverage advanced technologies like AI, machine learning, and automation to enhance threat detection, response, and prevention efforts.
Conclusion: Building Cyber Resiliency for Long-Term Protection
Achieving cyber resiliency is vital for ensuring that your organization can withstand and recover from cyberattacks with minimal impact. By focusing on prevention, detection, response, recovery, and adaptation, businesses can enhance their defenses and reduce the consequences of any cyber threat. A comprehensive cyber resiliency approach not only protects your organization from immediate risks but also ensures its long-term ability to adapt to an ever-changing threat landscape.
Building resilience against cyberattacks is an ongoing process that requires commitment, vigilance, and a proactive approach to security. By investing in these strategies, your organization can navigate cyber risks effectively while securing its future in an increasingly digital world.