In today’s digital world, where we manage finances, shop, and connect with just a few clicks, phishing remains a hidden yet pervasive threat. Unlike traditional cyberattacks that break through firewalls and infiltrate servers, phishing silently lurks, disguised as a legitimate message, waiting for you to unknowingly open the door.
Phishing is one of the most common ways cybercriminals deceive users into divulging sensitive information. This post explains how phishing attacks operate, the different types of phishing schemes, and practical steps to protect yourself from falling victim to them.
What is Phishing in Cybersecurity?
Phishing is a form of social engineering that uses deceptive communication methods—such as emails, phone calls, text messages, or websites—to trick individuals into sharing personal data, such as login credentials, financial details, or downloading malicious software. These attacks often impersonate trusted entities like banks, government organizations, or colleagues, making them difficult to detect. The primary aim is to gain unauthorized access to valuable personal or corporate information, which can lead to severe consequences.
The rise in phishing attacks is alarming. In 2023 alone, nearly 5 million phishing incidents were reported, marking a significant increase in the frequency and sophistication of these attacks. As phishing tactics evolve, both individuals and organizations need to understand the risks and take proactive steps to defend against them.
Phishing attacks can have devastating effects, including financial loss, identity theft, data breaches, and compromised systems. For individuals, the damage might include drained bank accounts or damaged credit scores. For businesses, the risks are far greater, with potential data leaks, financial losses, regulatory fines, and long-term reputational harm.
Common Types of Phishing Attacks
Phishing attacks come in various forms, each tailored to exploit specific vulnerabilities. Here are some of the most common types:
Email Phishing
The most widespread form of phishing, where attackers send fraudulent emails pretending to be legitimate organizations such as banks, retailers, or government bodies. These emails typically contain malicious links or attachments that, once clicked, can steal sensitive information or install malware on the victim’s device.
Spear Phishing
Unlike generic phishing, spear phishing is a targeted attack. Cybercriminals gather information about a specific individual, often through social media, to craft a convincing message that appears to come from a trusted source. This personalized approach increases the chances of the victim falling for the attack, often leading to significant security breaches.
Whaling
A more advanced form of spear phishing, whaling targets high-profile individuals, such as CEOs or CFOs. The emails in whaling attacks are designed to look incredibly authentic, often requesting sensitive corporate data or initiating financial transactions. These attacks are particularly dangerous due to their potential impact on entire organizations.
Vishing (Voice Phishing)
Vishing involves phishing attempts made over the phone. Attackers impersonate representatives from trusted organizations like banks or tech support and manipulate victims into revealing sensitive information such as Social Security numbers or account details. Vishing often relies on creating a sense of urgency to get victims to act quickly without questioning the legitimacy of the call.
Smishing (SMS Phishing)
Smishing is phishing carried out through text messages. Cybercriminals send SMS messages that look like they come from legitimate organizations, often containing links to malicious websites or phone numbers designed to steal personal information or install malware.
CEO Fraud (Business Email Compromise)
CEO fraud is a type of spear phishing where attackers impersonate a senior executive, often the CEO, and send an email to employees, particularly in the finance department, requesting money transfers or sensitive information. The email often seems legitimate due to the perceived authority of the sender.
Pharming
Pharming involves redirecting users from legitimate websites to fraudulent ones without their knowledge. This attack typically targets the Domain Name System (DNS), causing users to be redirected to malicious websites that capture login credentials and other personal data.
Social Media Phishing
Phishing can also occur on social media platforms. Attackers create fake profiles that impersonate friends, colleagues, or trusted brands to deceive users into providing personal information or clicking on harmful links. Angler phishing is a specific social media phishing technique that exploits the immediacy and trust built into social media interactions.
Clone Phishing
In clone phishing, attackers create a nearly identical copy of a legitimate email that the victim has received in the past. They then modify the email slightly, often adding a malicious link or attachment, and send it as a follow-up or update. Since the email looks familiar, the victim is more likely to trust it and engage with the harmful content.
How Phishing Works
Phishing attacks usually follow a structured approach designed to manipulate victims into sharing their sensitive information or performing actions that compromise their security. Here’s how the typical phishing attack unfolds:
Exploiting Human Error
Phishing relies heavily on social engineering, exploiting human emotions like fear, curiosity, or urgency. Attackers craft messages designed to bypass a person’s skepticism and manipulate them into taking actions that undermine their security.
Malicious Messaging
The attack often starts with a message that appears legitimate—whether it’s an email, text, or social media post. Cybercriminals mimic the branding, tone, and style of trusted organizations to deceive victims into engaging with the message. The goal is to bypass initial skepticism and get the recipient to take action.
Information Theft
Phishing messages often create a sense of urgency, prompting victims to act quickly—whether it’s by warning them that their account is compromised or offering a limited-time opportunity. This urgency prevents individuals from critically evaluating the message, leading them to click on a malicious link or submit personal information.
Evolving Tactics
Phishing tactics continuously evolve to adapt to new security measures. As email filters and security monitoring tools improve, cybercriminals refine their strategies to bypass these defenses. Attackers now use more sophisticated methods to avoid detection, making constant awareness and training essential for staying protected.
Phishing Techniques
Phishing attacks are carried out using several techniques designed to deceive victims into revealing their personal information. Some of the most common methods include:
Malicious Web Links
Phishing emails often contain links that appear to lead to legitimate websites. In reality, these links redirect victims to fake sites designed to steal login credentials, payment details, or other sensitive data.
Malicious Attachments
Phishing emails may also include attachments that, when opened, install malware on the victim’s device. These files are often disguised as important documents like invoices or official forms.
Fraudulent Data-Entry Forms
Attackers create fake websites that look like legitimate portals, such as banking sites or e-commerce platforms. These sites host data-entry forms designed to collect personal information from unsuspecting victims.
How to Spot a Phishing Email
Identifying phishing emails can be tricky, especially as attackers become more sophisticated. However, there are common signs to look for, such as misspelled words, odd sender addresses, or suspicious links. Being able to spot these signs is crucial for protecting your personal information.
Protecting Against Phishing
The best defense against phishing is a combination of education and robust cybersecurity systems. Here’s how to protect yourself and your organization:
Security Awareness Training
Education is the first line of defense. Regular security training, including phishing simulations, helps employees recognize phishing attempts and understand how to respond to them.
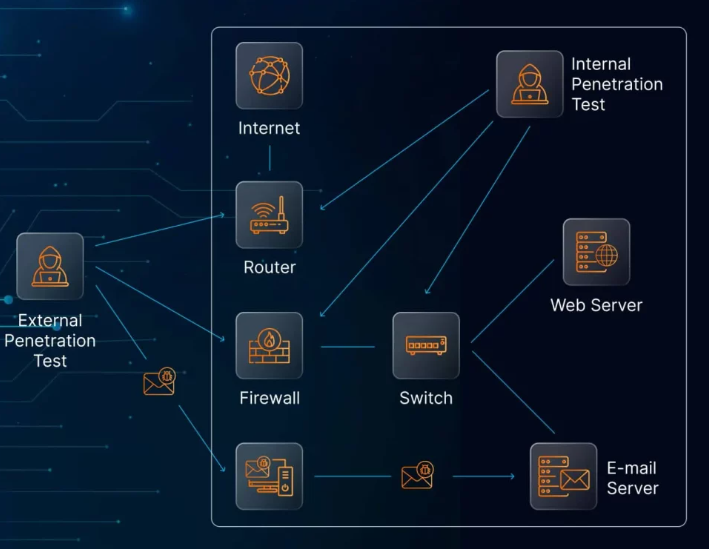
Cybersecurity Systems
Strong cybersecurity tools, such as antivirus software, firewalls, and multi-factor authentication (MFA), are essential for preventing phishing attacks. These systems can help detect phishing emails before they reach your inbox and block harmful links.
Organizational Policies
Establish clear policies, such as mandatory MFA and regular security audits, to reduce the risk of successful phishing attempts. Having clear reporting procedures in place ensures that any phishing attempts are flagged quickly.
Real-World Phishing Scams
Phishing scams occur frequently in the real world, often targeting both individuals and organizations. These attacks are carefully crafted to exploit specific vulnerabilities, making them highly effective. Examples include:
- Digital Payment Scams: Scammers impersonate legitimate payment services and trick victims into providing payment details on fake websites.
- Finance-Based Phishing: Attackers impersonate banks or financial institutions to steal sensitive financial data.
- Work-Related Scams: In corporate settings, phishing is used to impersonate HR departments or executives in order to gain access to sensitive company data.
The Future of Phishing
As technology advances, so do phishing tactics. The use of AI and deepfake technology is making phishing attacks even more convincing. To stay ahead of these evolving threats, it’s crucial to maintain continuous vigilance, up-to-date security measures, and ongoing training for all employees.