In today’s digital environment, cyber threats are no longer a distant concern—they’re an everyday reality for businesses of all sizes. From data breaches to ransomware attacks, the potential consequences of a weak security posture can be devastating. Yet, many organizations still take action only after an incident occurs. A smarter strategy is to identify and address risks before they turn into crises, and that’s where cybersecurity risk assessments come in.
What Is a Cybersecurity Risk Assessment?
A cybersecurity risk assessment is a strategic process designed to evaluate how well your systems, data, and operations are protected against potential threats. It involves identifying key assets, analyzing vulnerabilities, and determining the likelihood and impact of different risks. The goal is to understand where you’re exposed and implement appropriate measures to reduce those risks.
In essence, it’s like a check-up for your digital infrastructure—making sure your security defenses are aligned with your actual risk landscape.
Why Routine Risk Assessments Are Essential
1. Adapting to a Rapidly Evolving Threat Environment
Cybercriminals are constantly refining their tactics. From phishing emails to ransomware and zero-day exploits, the tools they use grow more sophisticated by the day. Regular risk assessments help businesses stay ahead by identifying weak points before attackers do.
2. Meeting Regulatory Standards
Laws and industry standards like GDPR, NIS2, and ISO 27001 demand robust cybersecurity practices. Conducting assessments helps ensure compliance, avoid fines, and demonstrate accountability to regulators and stakeholders.
3. Aligning Security with Business Priorities
With limited resources, security investments need to be strategic. Risk assessments guide decision-making by showing where vulnerabilities pose the most danger, allowing organizations to focus their budgets where they’ll have the greatest impact.
Different Approaches to Risk Assessment
Depending on your objectives, industry, and infrastructure, different types of risk assessments can be used:
- Qualitative Assessments: Use risk matrices to evaluate threats based on likelihood and severity. Ideal for quick, high-level overviews.
- Quantitative Assessments: Assign monetary values to risks, helping calculate the financial impact of potential incidents.
- Compliance-Focused Assessments: Compare current practices against regulatory requirements to identify compliance gaps.
- Threat-Centric Assessments: Focus on real-world adversary tactics and techniques to assess readiness for evolving threats.
- Vulnerability-Based Assessments: Identify and analyze technical flaws such as misconfigurations or outdated systems.
- Third-Party Assessments: Evaluate the cybersecurity practices of vendors and partners, especially those with access to sensitive data.
- Business Impact Analyses: Determine how different incidents would disrupt operations and guide business continuity planning.
- Cybersecurity Maturity Assessments: Use established frameworks to benchmark current capabilities and create a roadmap for improvement.
Five Key Steps to Conducting a Risk Assessment
1. Define and Locate Critical Assets
Start by identifying the systems, data, and services that are vital to your business. This includes customer records, intellectual property, operational platforms, and any third-party tools that interact with sensitive data.
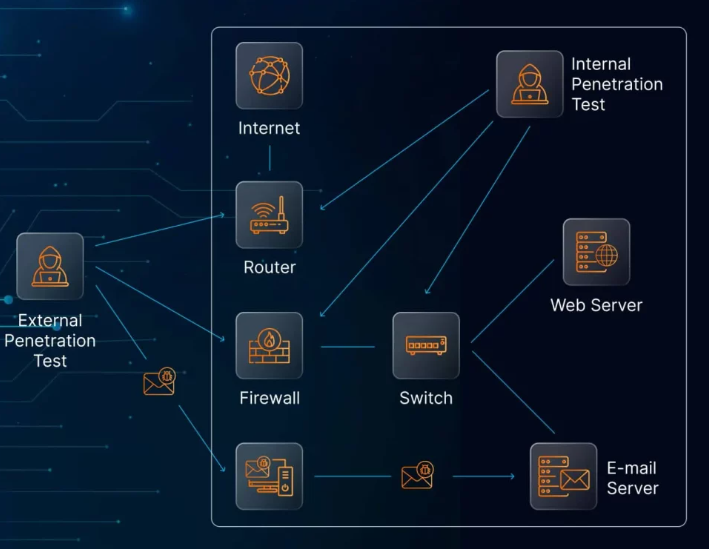
2. Identify Threats and Vulnerabilities
Once your critical assets are mapped out, analyze the potential threats that could affect them. These include both external threats (such as malware or DDoS attacks) and internal risks (such as employee errors or insider misuse). Tools like vulnerability scanners and security audits can assist in uncovering weak points.
3. Evaluate Risk Likelihood and Impact
Not every threat is equally urgent. Assign scores to each identified risk based on how likely it is to occur and how damaging it could be. This structured approach helps prioritize efforts and resource allocation.
4. Choose a Risk Response Strategy
Decide how each risk should be addressed. The options include:
- Avoiding the risk altogether
- Mitigating it through controls like encryption or access management
- Transferring it via cyber insurance or outsourced services
- Accepting the risk if the potential impact is minimal
Your strategy should align with business goals and available resources.
5. Monitor and Reassess Continuously
Cybersecurity is never static. New vulnerabilities emerge, technologies evolve, and business needs change. Periodic reassessments and continuous monitoring are essential to maintaining a strong security posture.
Common Roadblocks and How to Overcome Them
Limited Internal Expertise
Many businesses don’t have in-house specialists to conduct thorough assessments.
Solution: Partner with cybersecurity consultants or use virtual CISO services to access experienced professionals without long-term overhead.
Time and Budget Pressures
Organizations often delay risk assessments due to cost or resource constraints.
Solution: Automate parts of the process using tools like vulnerability scanners and threat intelligence platforms to save time and reduce costs.
Poor Risk Prioritization
Misjudging which threats matter most can lead to wasted efforts.
Solution: Rely on proven frameworks such as NIST or CIS Controls to evaluate and rank risks accurately based on data, not guesswork.
Conclusion
Cybersecurity risk assessments aren’t just about ticking a compliance box—they’re a vital tool for protecting your business from real-world threats. By regularly identifying and addressing vulnerabilities, companies can avoid the high costs of breaches, maintain customer trust, and ensure operational continuity.
The digital world is unpredictable, but a structured approach to risk can give your organization a critical edge. Make risk assessments a recurring part of your strategy, not just an occasional exercise. Your resilience depends on it.