In the race to deliver cutting-edge software and deploy updates at lightning speed, security can easily take a back seat. For software companies, this oversight isn’t just risky—it can be disastrous. As development cycles accelerate and digital ecosystems grow more complex, the exposure to cyber threats increases in tandem.
Today, software businesses are frequent targets for cybercriminals. Their platforms often store sensitive information, manage critical transactions, and depend on third-party integrations—all of which can open the door to attackers if not properly secured. One small vulnerability could escalate into a full-scale breach, compromising customer data, damaging brand reputation, or triggering regulatory consequences.
To safeguard against these risks, penetration testing has become essential. Far beyond routine scans, it mimics real attack scenarios to find and exploit weaknesses before malicious actors do. For companies that develop software, integrating penetration testing into operations is a necessary step toward long-term resilience and customer trust.
Unique Challenges in Software Development
Unlike many industries, software companies are in the business of creating technology rather than just using it. Their digital infrastructure is constantly evolving—new code is deployed regularly, integrations shift, and user-facing features are in constant flux. With such agility comes increased exposure to security flaws.
From improperly secured APIs and insecure authentication methods to overlooked staging environments and third-party services, threats can emerge at any phase of development. The rapid pace often outstrips traditional security practices, leaving teams with little time to assess the full risk of each change.
Cybercriminals take advantage of this. According to recent industry data, exploitation of software vulnerabilities surged dramatically in the past year, becoming one of the top causes of data breaches globally. As software continues to underpin everything from e-commerce to finance, it’s become a prime hunting ground for attackers.
The Value of Penetration Testing
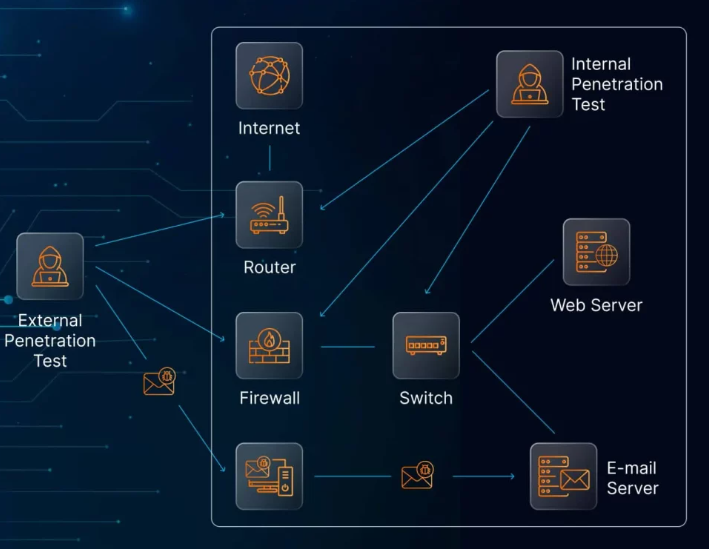
Penetration testing goes beyond identifying potential risks—it demonstrates how those weaknesses could be used in real-world attacks. For software developers, this means simulating a threat actor’s path through an application, from finding initial entry points to escalating privileges or accessing sensitive information.
These assessments test the security of:
- Application logic and session handling
- Authentication flows and access controls
- Cloud and infrastructure configurations
- APIs, integrations, and third-party components
- Source code and development environments
The advantage isn’t just technical. Penetration testing also supports key business outcomes:
- Protecting users and reputation: Data breaches erode customer confidence. Regular testing helps avoid the kind of high-profile incidents that drive users away.
- Meeting compliance expectations: Most industry standards—such as ISO 27001, PCI DSS, and DORA—require evidence of security testing.
- Enabling secure development: Test findings offer valuable input for developers, helping them write more secure code and address vulnerabilities early.
- Supporting customer acquisition: Enterprise clients increasingly ask for proof of cybersecurity maturity. A penetration test report shows you’re serious about security.
- Reducing long-term risk and cost: Identifying and resolving security flaws during development prevents expensive fixes or data recovery efforts later on.
When to Perform Penetration Testing
Treating penetration testing as a one-time event is a common mistake. To be effective, it needs to be part of an ongoing security strategy—closely tied to development milestones and operational changes.
Key times to conduct testing include:
- Prior to major releases: Launching a new product or deploying a significant update is a natural trigger for a security check.
- After major infrastructure changes: Whether migrating databases or changing API structures, technical shifts often introduce new risks.
- Following suspicious activity: If there’s been a security incident or even unusual system behavior, penetration testing helps uncover lingering vulnerabilities.
- On a recurring basis: Quarterly or biannual assessments ensure consistent oversight as platforms scale and threats evolve.
Forward-thinking teams are also integrating testing earlier in the development process—a strategy known as “shift-left security.” This means identifying weaknesses during design and coding phases rather than waiting until deployment. By embedding security into the development lifecycle, companies can stay ahead of risks while maintaining delivery speed.
Finding the Right Testing Partner
The effectiveness of a penetration test depends heavily on who performs it. Software-focused companies should seek testers who understand the intricacies of development environments—not just traditional IT systems.
When selecting a provider, look for:
- Relevant technical expertise: Choose a team familiar with your tech stack, frameworks, and common vulnerabilities in modern software.
- Customized testing plans: A good testing partner tailors their approach to your specific product architecture and threat profile.
- Certified professionals: Trust testers who hold recognized credentials and adhere to ethical standards.
- Detailed, actionable results: Reports should clearly explain each issue, its potential impact, and practical recommendations for fixing it.
- Ongoing support: The right partner helps your team remediate issues, not just document them.
Generic testing solutions and automated-only assessments often miss context-specific vulnerabilities. Software platforms are unique by nature, and their security testing should be as well.
Final Thoughts
Software companies today face mounting pressure to move fast, innovate constantly, and ensure airtight security—all at once. This balancing act is challenging, but not impossible.
Penetration testing offers a practical way to meet these demands. By simulating how attackers might target your applications, systems, and infrastructure, it gives development and security teams the insights they need to reduce risk and build trust.
Security isn’t just a checkbox—it’s a foundation for sustainable growth. As software becomes more central to our lives and work, companies that invest in rigorous, ongoing testing will be the ones best positioned to thrive in an increasingly hostile digital landscape.